From Purchase Order to Goods Receipt: The Risk Created by “One-Person Control” — The Data Already Knows
- Apr 9
- 2 min read

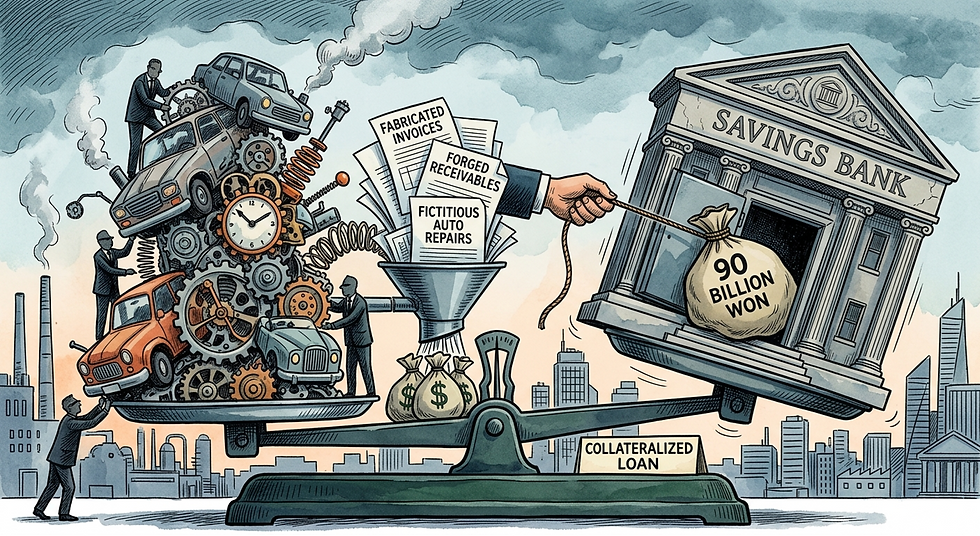
Fraud and embezzlement often begin in surprisingly simple processes.
A recently reported embezzlement case involving manipulated material orders at a large company in Gwangju illustrates the kinds of risks that can arise when purchasing, inventory, and inspection processes are not properly segregated, or when data-driven monitoring is weak.
According to media reports, the employee responsible for material ordering allegedly exploited a structure in which the same person had both the authority to arbitrarily adjust inventory quantities and responsibility for inspection. By doing so, the employee was accused of making materials that were never actually delivered appear as though they had been normally ordered and consumed, while routing funds through a supplier to a family-owned business. A heavy prison sentence was ultimately imposed.
The core issue in this case is not merely individual misconduct.
It is a control failure across the full flow of purchase orders (PO), goods receipt (GRN), invoices, inventory, inspection, and vendor activity.
From a practical standpoint, risks of this kind often begin with questions such as these:
Are mismatches between PO, GRN, and invoices occurring repeatedly?
Are there cases of billing without actual receipt of goods, or overbilling relative to goods received?
Is the same person repeatedly adjusting inventory quantities for the same items?
Are inventory adjustments relying on after-the-fact explanations rather than sufficient supporting evidence?
Are transactions overly concentrated between a specific employee and certain vendors?
Are purchase ordering, inventory modification, inspection, and vendor communication all concentrated in the hands of one person?
These warning signs do not become visible only after an incident occurs.
When transaction data and operational logs are reviewed, many of these signals can already be seen as recurring patterns well before the case comes to light.
For example, the following data-driven checks can be useful in identifying similar risks in advance:
Mismatch patterns among PO, GRN, and invoices
Overbilling relative to actual receipt, or transactions with no goods received
Repeated inventory adjustments and quantity changes
Inventory adjustments made without sufficient supporting evidence
Transaction structures heavily concentrated between a specific employee and a vendor
Ultimately, the key message is clear.
Before fraud becomes visible as an incident, it often appears first as a pattern in the data.
By analyzing purchasing, goods receipt, invoices, inventory, approvals, and user logs together,
GRAM Radar helps identify early red flags such as:
fictitious purchase orders
billing without physical delivery
repeated inventory adjustments
unsupported adjustments
concentration between a specific employee and vendor
What matters far more than explaining a problem after it happens is checking for the signals before it occurs.
That is exactly why a proactive, data-driven Quick Scan is valuable from the perspectives of internal audit, procurement, finance, and management oversight.
Have you ever seen similar patterns in practice?